Details
-
Bug
-
Resolution: Fixed
-
Critical
-
None
-
None
-
3
-
9223372036854775807
Description
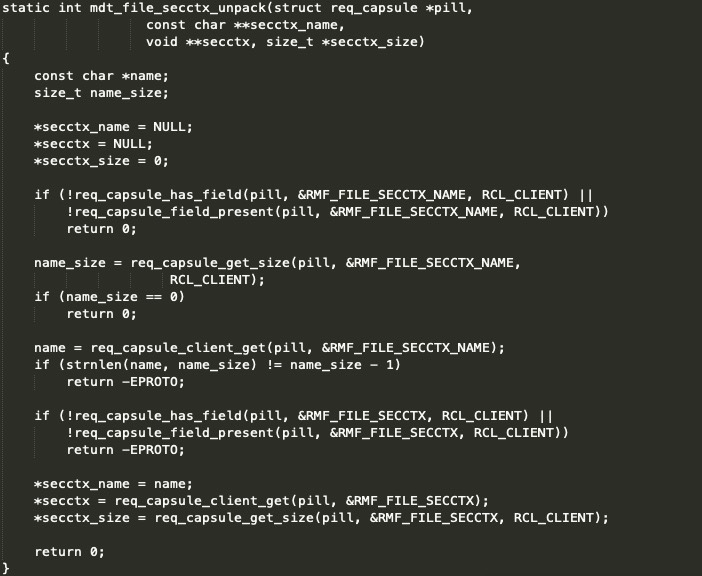
In the latest version of lustre file system, mdt module has a out-of-access bug due to the lack of validation for specific fields of packets sent by client.
The kernel panic:
[ 207.996447] Call Trace: [ 207.998174] [<ffffffffc0fc12d6>] mdt_file_secctx_unpack+0xb6/0x140 [mdt] [ 208.000279] [<ffffffffc0fc6ecc>] mdt_open_unpack+0x19c/0x410 [mdt] [ 208.002318] [<ffffffffc0fc71eb>] mdt_reint_unpack+0xab/0x210 [mdt] [ 208.004342] [<ffffffffc0fb0d23>] mdt_reint_internal+0x43/0xb90 [mdt] [ 208.006379] [<ffffffffc0fbd8e0>] ? mdt_intent_fixup_resent+0x160/0x220 [mdt] [ 208.008481] [<ffffffffc0fbda22>] mdt_intent_open+0x82/0x3a0 [mdt] [ 208.010505] [<ffffffffc0697b49>] ? lprocfs_counter_add+0xf9/0x160 [obdclass] [ 208.012619] [<ffffffffc0fbb9e4>] mdt_intent_policy+0x2d4/0xdd0 [mdt] [ 208.014675] [<ffffffffc0fbd9a0>] ? mdt_intent_fixup_resent+0x220/0x220 [mdt] [ 208.016810] [<ffffffffc08a3c66>] ldlm_lock_enqueue+0x356/0xa20 [ptlrpc] [ 208.018833] [<ffffffffc052f3d3>] ? cfs_hash_bd_add_locked+0x63/0x80 [libcfs] [ 208.020881] [<ffffffffc053296e>] ? cfs_hash_add+0xbe/0x1a0 [libcfs] [ 208.022874] [<ffffffffc08cc587>] ldlm_handle_enqueue0+0xa47/0x15a0 [ptlrpc] [ 208.024948] [<ffffffffc08f4520>] ? lustre_swab_ldlm_lock_desc+0x30/0x30 [ptlrpc] [ 208.027041] [<ffffffffc0955082>] tgt_enqueue+0x62/0x210 [ptlrpc] [ 208.028973] [<ffffffffc095b2ca>] tgt_request_handle+0x91a/0x15c0 [ptlrpc] [ 208.030903] [<ffffffffc052bfa7>] ? libcfs_debug_msg+0x57/0x80 [libcfs] [ 208.032796] [<ffffffffc08fe88e>] ptlrpc_server_handle_request+0x24e/0xab0 [ptlrpc] [ 208.034745] [<ffffffff8eccbadb>] ? __wake_up_common+0x5b/0x90 [ 208.036513] [<ffffffffc0902384>] ptlrpc_main+0xbb4/0x20f0 [ptlrpc] [ 208.038274] [<ffffffff8ecd08c0>] ? finish_task_switch+0x50/0x1c0 [ 208.040036] [<ffffffffc09017d0>] ? ptlrpc_register_service+0xfa0/0xfa0 [ptlrpc] [ 208.041892] [<ffffffff8ecc1c71>] kthread+0xd1/0xe0 [ 208.043535] [<ffffffff8ecc1ba0>] ? insert_kthread_work+0x40/0x40 [ 208.045284] [<ffffffff8f375c1d>] ret_from_fork_nospec_begin+0x7/0x21 [ 208.047012] [<ffffffff8ecc1ba0>] ? insert_kthread_work+0x40/0x40
In function mdt_file_secctx_unpack(), it don't check the value of name_size derived from req_capsule_get_size(), and cause a out-of-access bug in strnlen.
Attachments
Issue Links
- is related to
-
LU-12605 Lustre target_handle_connect() bug
-
- Resolved
-
